Hyas Blog | Why We Still Haven’t Learned from the Target Data Breach Years Later
The threat actor’s methodology wasn’t unique — they used a six-step approach that can be mapped directly to cyber attack frameworks. Most of these steps could’ve been blocked with the aid of DNS protection.
With cybercrime at record levels, businesses are on guard against a constantly growing number and variety of threats. But even as companies race to increase cybersecurity spending and awareness, data breaches have actually become much more (not less) likely. It would be easy to chalk up this increase to the development and introduction of new advanced types of malware, but the surprising fact is that many of the same threats and exploits used in data breaches in 2013 are still being successfully employed 10 years later.
Even industry giants like Target and Equifax, who have robust security measures, still struggle to combat supply chain attacks. Small and mid-sized businesses are faced with the same problems, yet must also contend with being under-resourced, under-funded, and under-staffed. That’s why so many businesses today are still in position to fall victim to the same types of attacks that were so successful a decade ago.
To be able to finally tackle the real work implementing proper threat protection, it’s crucial to know exactly what happened. More importantly, businesses need to understand how the event could (and should) have been protected against to be able to avoid the same fate.
Tales From the Breach: What Organizations Are (and Aren’t) Doing
The 2013 Target data breach was a watershed moment within the cybersecurity landscape. So much so that you would be hard-pressed to find anyone in the industry who hasn’t at least heard of it. During the attacks, 110 million customers had their credit and debit card data exposed by a threat actor who managed to gain access to nearly all of their point of sale (PoS) data.
But in the wake of the well-publicized attack, how many organizations actually took the requisite steps to protect themselves against the same sort of data breach? In truth, we may never know.
The Target breach was not carried out as a direct attack against Target’s PoS infrastructure. Rather, the bad actor infiltrated Target’s systems via its heating, ventilating, and air conditioning (HVAC) system — a vulnerability that exploited a trusted third party to get into Target’s system. It’s a reminder that no matter how good your defenses are, bad actors will eventually find some way in, a lesson that is even more salient today than in 2013.
Perhaps one of the most frustrating things of the Target breach — besides the fact that large businesses are still vulnerable to the same kind of attack — is that the threat actor was never identified. While Target was forced to pay out a settlement to customers affected by the attack, the person/s who initiated the attack will never face justice.

How it Went Down: Target’s Breach in 6 Steps
The Target situation is a valuable real-world example of a cyber kill chain in action. Though we still don’t know the identity of the attacker(s), we know they carried the attack in six basic steps.
Step 1: Gathering Information
Reconnaissance is the first step of the cyber kill chain. If you’re a cyber attacker, the first thing you want to do is gather information to learn as much as possible about your target. This can include network probes, infrastructure mapping, and searching for unpatched vulnerabilities that the bad actor can use to conduct their attack.
In this case, the threat actor is thought to have directly pulled details from a Microsoft report on Target and how it deployed its virtualized servers. This document revealed Microsoft System Center as Target’s endpoint and point of sale (POS) management tool.
Furthermore, Target’s supplier portal — though protected by an account login — hosted some of its materials in publicly accessible areas. Suppliers had to log in to work with Target, but its tutorial materials were viewable even to those without an account. The threat actor was able to view these tutorials and learn about the company’s systems in detail. It’s in this documentation that they found the details regarding the HVAC companies used by Target.
Step 2: Compromising a Third-Party Vendor
The attacker conducted a spear phishing attack and sent an email that appeared to be from a known entity. An employee at one of the HVAC companies opened the email and clicked on the malicious attachment, which caused malware to deploy on the employee’s PC.
To reiterate, this was not a Target employee but a third-party associate. The malware itself wasn’t particularly sophisticated, either. It was an old strain that would normally be detected by most antivirus and endpoint detection and response (EDR) vendors. But the third-party company was using a free version of Malwarebytes with only on-demand — rather than real-time — scanning capabilities. The system wasn’t scanned, and the malware was able to deploy with ease.
Step 3: Gaining an Initial Foothold
The malware logged the credentials and sent them to the threat actor to access the Target supplier portal at will. The portal used the Ariba billing system, which is believed to have been exploited to gain active directory (AD) credentials. In 2013, Ariba had known vulnerabilities, and using an SQL injection attack to gain access to the system wouldn’t have been difficult.
Depending on access level, the attacker may have escalated privilege and ultimately created persistent access. This is important if targets patch exploits, removing attacker access. This may have been a reverse shell or command and control (C2) server-based communication.
Step 4: Moving Laterally
Once the attacker gained an initial foothold, they did some lateral movement. Ultimately, multiple internal Windows servers were compromised. This almost certainly included access to Microsoft System Center, which can in turn be used to manage more systems to bring attackers closer to their objective.
Step 5: Infecting POS Systems
The POS systems didn’t have access to the Internet themselves. So how did the attacker gain access?
It’s probable that they used Microsoft System Center to easily push malware — in this case Trojan.POSRAM — and extract credit and debit card information from memory while they were being swiped. The process involves encryption and decryption prior to verifying transactions. During the decryption, the malware reads and saves card information to a winxml.dll file.
Because it masks itself as a Windows system file, the winxml.dll doesn’t look out of place and is locally stored. No one examines it further.
Step 6: Exfiltrating the Data
The attacker gathered the data, which meant the next step was to get it back out and into the hacker’s hands.
The threat actor most likely copied the winxml.dll file to an internal host on the Target network — one also breached during step four — as a dump server. They then sent a special Internet Control Message Protocol (ICMP) packet to a remote server — such as an attack control server — to inform operators that the target data now resided on this dump server.
These operators are then able to move the data from the internal dump server to remote FTP servers also controlled by the threat actor.
How Might the Target Breach Have Been Prevented?
Not every data breach will follow these steps, but many likely will.
It’s difficult to prevent information gathering completely, but not impossible. Companies can (and should) be more cautious about what they’re publicizing on the Internet and who might have potential access to sensitive information.
Let’s say a threat actor does gain some information that makes you vulnerable. There are still many opportunities to thwart an attack at the DNS level. In Target’s case, protective DNS, such as HYAS Protect, could have prevented the attack from advancing during at least four steps. Here’s how:
- The spear phishing attack (Step 2) wouldn’t be prevented entirely, but HYAS Protect would have alerted administrators or outright blocked communication with the malicious domain set up to harvest the credentials entered by the victim.
- While the billing system exploit (Step 3) or privilege escalation wouldn’t have been visible, HYAS protective DNS would have spotted the persistent access by tracking adversary infrastructure communication — leading to detection, alert, and easy blocking.
- Using HYAS Confront for a production network notifies customers of unusual and off-baseline server communications (Step 4). They can then investigate and block unwanted activity.
- If by some chance the attacker was able to make it to exfiltration stage (Step 6), the infrastructural communication would again be visible and easily blocked.
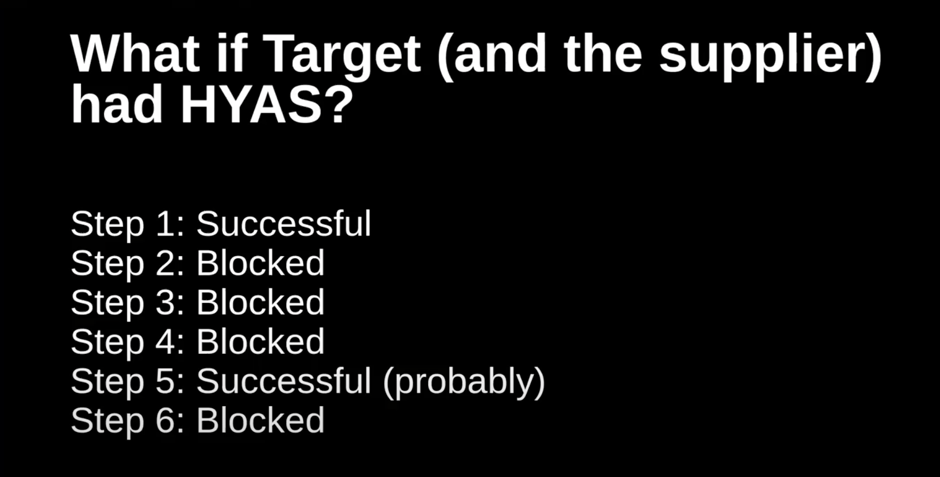
The threat actor’s POS system work with Microsoft System Center at Step 5 was sophisticated. But HYAS would have caught and blocked the threat at all prior steps following reconnaissance, prior to and including exfiltration — which would not happen.
Learning from the Past
The fact that the same threat that hit Target 10 years ago is still a risk today highlights the urgency with which businesses need to take the right steps to protect themselves. The Target attack highlights the fact that no matter how strong your perimeter defenses are, there will always be vulnerabilities that cannot be planned for. However, by monitoring communications at the DNS level for behavior common to nearly all forms of malware, you can take advantage of a more proactive approach to security.
Although awareness and knowledge have grown, it is time to raise protection to the same level. Protective DNS is a mission-critical priority for all businesses that want to ensure they can confidently face the ever-evolving threat landscape, reassured they are fortified with the best protection available to run their operations.
Are you ready to protect yourself in a more dangerous cyber landscape? Move your business forward with HYAS today.
