Hyas Blog | Anatomy of a Ransomware Attack
Ransomware has been an ongoing scourge to enterprises and is getting increasing coverage in mainstream media. While there are recent headlines around enterprises like Colonial Pipeline and Scripps Health, ransomware has been around for quite some time and changed over the years. Ransomware has evolved from targeting individual computers to more recently locking the files of entire enterprises and demanding multi-million dollar ransoms which are often paid.
Today, ransomware has become one of the primary interests of criminal enterprises and it has developed a sort of criminal “support industry” around it that offers access to large corporations, selling credentials for remote access tools, and laundering cryptocurrency. Ransomware operators often participate in criminal forums and Telegram groups where cybersecurity threat analysts can frequently monitor their discussions, offers, and disputes and mine them for data that is helpful for understanding how they operate.
Locked and Extorted
The earliest forms of ransomware were typically introduced using a chain involving the exploitation of vulnerabilities in web browsers and installed plug-ins using so-called exploit kits. Although exploit kits still exist today, their use is far less common because the frequency of new vulnerabilities becoming available is not high enough to support the effort. Automated patching in browser systems and sandboxing have made it more difficult to exploit vulnerabilities than it once was.
Today, ransomware is primarily introduced to victim machines either by malware that is delivered by Microsoft Office documents containing malicious macros or it is introduced by someone manually from a machine that has had remote access enabled such as remote desktop protocol (RDP) or Citrix credentials guessed or compromised via a brute force attack. The availability of RDP accounts in particular is significant and crime markets like UAS make it simple to find and purchase credentials for servers anywhere in the world for around $US10-$US25.
(UAS online criminal market screenshot)
Once a foothold is established on a victim machine, criminals affiliated with the ransomware will explore the network to list all available resources. If they’re able to find potentially sensitive data on file shares, it may be exfiltrated to a cloud service. In many incidents, additional malware families are used including Trickbot, Cobalt Strike, and various multipurpose tools such as password recovery programs. One of the final steps is typically to create an automation script that will deploy the ransomware to as many surrounding machines as possible. Many malware families work entirely offline, so the payload, ransom note, and communication instructions are pre-configured prior to the ransomware’s insertion into the victim network. This leaves fewer opportunities for disruption and prevention by enterprises.
Recommendations
- Control Microsoft Office Macros - Many of the successful ransomware operations make use of a well-known pattern of compromise starting with the delivery of malicious Microsoft Office documents containing macros that entice a recipient into enabling content that drops a malicious payload. This malicious payload may collect data about the machine, report back to a command and control (C2) domain, and then download and execute additional malware modules. Preventing the execution of malicious Office macros is an effective approach to preventing the introduction of many malware families that lead to ransomware. Enterprises using Microsoft Office can configure it so that macros that were downloaded from the Internet or from an email attachment cannot be run. A best practice for enterprises concerned about malware is to not leave the decision to execute macros up to the recipient.
- Multi-factor Authentication for RDP, Citrix & VPN - Many enterprises that have become victims of ransomware were compromised because they left RDP or Citrix exposed to the Internet and criminals gained access to it either by purchasing the account from a crime market, finding it in the logs of stealer malware, or the criminals brute-forced the credentials themselves. Remote access tools such as RDP, Citrix, and VPNs should not be exposed without multi-factor authentication (MFA). RDP and Citrix can often be configured behind a firewall that limits the access to IP ranges belonging to designated business partners.
- Backup, Backup, Backup - One problem victims have expressed is that they did in fact have backups of their data to restore but it would have taken so long to recover their systems from backups that they felt the only choice they had was to pay the ransom. Preparing for disaster and continuity should consider the possibility of ransomware and how to recover from it fast enough to avoid giving millions of dollars to a criminal enterprise.
- Validate Your Supply Chain - One less common avenue for compromise comes from compromised accounts in cloud management tools often used by managed service providers (MSPs). Any service or system that provides persistent access like this should require multi-factor authentication.
- Monitor Criminal Marketplaces and Infrastructure - Criminal attackers need to stage command and control infrastructure as well as broker access in criminal marketplaces. Threat intelligence can provide insights into what attackers are staging and what credentials might be in play. Monitoring criminal markets for potential breach exposure before access is sold enables enterprises to avoid a potential breach
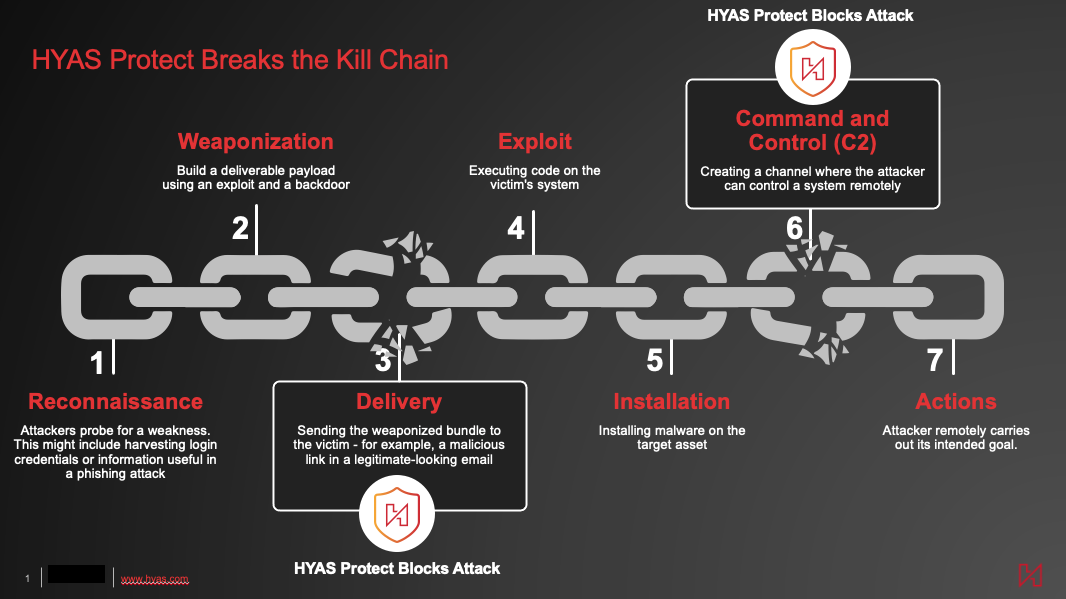
- DNS for Visibility & Blocking Command and Control Communication - One commonality of many ransomware attacks involves external communication using the domain name system (DNS) to lookup/resolve the C2 destination. Malware frequently needs to communicate with a C2 domain to receive commands from the threat actor, such as download additional malicious tools or exfiltrate data. All of this traffic utilizes DNS, and that DNS traffic represents a valuable source of threat intelligence. For most enterprises, DNS traffic is an under-appreciated and under-utilized source of threat intelligence.
HYAS Can Help
As ransomware communicates to its command and control, DNS network traffic provides a chokepoint where communication to malicious destinations can be blocked. HYAS Protect is a protective DNS solution providing a generational leap forward utilizing authoritative knowledge of attacker infrastructure to proactively protect organizations from cyberattacks. HYAS Protect is deployed as a cloud-based protective DNS security solution or through API integration with your existing security solutions. It leverages our infrastructure expertise and communication pattern analysis to block DNS connections from the precursor malware that leads to ransomware. To understand how you can counter ransomware by leveraging your organization’s existing DNS traffic with help from HYAS Protect, give us a shout.
…
