Threat Hunting Solutions
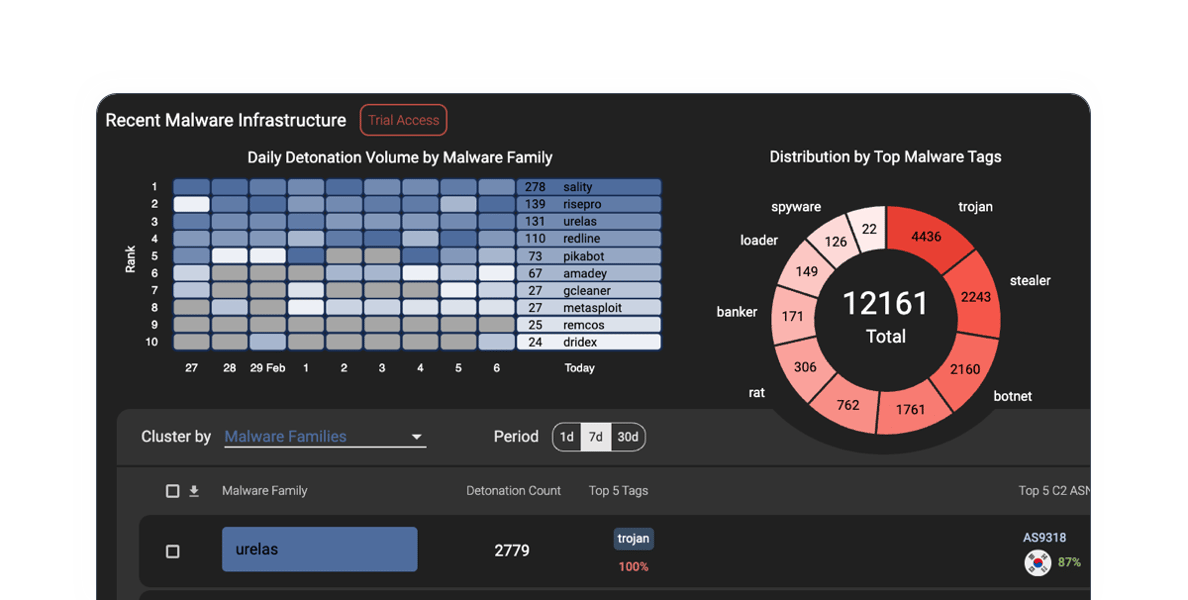
Our flagship product, HYAS Insight, is designed to empower cyber security professionals with advanced threat hunting tools and investigative capabilities to enable security teams to stay ahead of adversaries and proactively protect organizations.

Why Choose HYAS
As one of the top threat hunting platforms, HYAS Insight equips cyber security professionals with unparalleled threat intelligence and investigative capabilities, enabling proactive defense against even the most elusive adversaries.
Comprehensive Threat Intelligence
HYAS Insight offers access to a vast repository of threat data collected from diverse sources, providing you with comprehensive insights into emerging threats and malicious actors.
Advanced Investigation Tools
Equipped with state-of-the-art investigation tools, HYAS Insight enables you to conduct in-depth analyses of cyber incidents, identify root causes, and trace threat actors with unparalleled precision.
Real-Time Threat Monitoring
Stay ahead of threats with real-time monitoring capabilities that alert you to suspicious activities and potential security breaches, allowing for proactive threat mitigation.
Intuitive User Interface
Designed with usability in mind, HYAS Insight features an intuitive user interface that streamlines the investigative process, making it accessible to cybersecurity practitioners at all levels of expertise.
Customizable Workflows
HYAS Insight can be tailored to meet your organization's unique requirements and needs with customizable workflows and automated processes to optimize performance.
Optimize Efficiency and Productivity With HYAS Insight
Our advanced platform equips cyber security professionals with unparalleled threat intelligence and investigative capabilities, enabling proactive defense against even the most elusive adversaries. With our threat hunting tools, you can stay ahead of evolving threats, identify malicious actors with precision, and safeguard your organization's digital assets with unwavering confidence.

Threat Hunting With HYAS Insight
SANS Institute outlines how HYAS Insight enables security organizations to make the most of their available threat hunting resources, complete more threat hunts, and close more cases. HYAS packages intelligence in highly adaptable and customizable formats that are accessible and actionable for both sophisticated threat hunters and less skilled security practitioners.
/SANS_Institute_logo_575x375.png?width=575&height=375&name=SANS_Institute_logo_575x375.png)
BlackMamba
The BlackMamba proof-of-concept is an AI-synthesized, polymorphic keylogger with on-the-fly program modification. Our proof-of-concept (PoC) demonstrates that LLMs can be exploited to synthesize polymorphic keylogger functionality on-the-fly, making it difficult for EDR to intervene. The PoC exploits a large language model to synthesize polymorphic keylogger functionality on-the-fly, dynamically modifying the benign code at runtime and all without any command-and-control infrastructure to deliver or verify the malicious keylogger functionality. This technique runs unimpeded by EDR intervention.
/BlackMamba_no_text_575x375.png?width=575&height=375&name=BlackMamba_no_text_575x375.png)
EyeSpy Fully Autonomous Malware
As part of our continuing research, HYAS released EyeSpy, a proof-of-concept (PoC) for an entirely new type of AI-synthesized, polymorphic, and fully autonomous malware. The malware utilizes artificial intelligence to make informed decisions and synthesize its capabilities as needed to conduct cyberattacks and continuously morph to avoid detection. This malware isn’t just a program—it is an adaptive entity with evolving strategies, making it an ever-present, dynamic threat that evades detection.
/MIXEDEYE_1_575x375.jpg?width=575&height=375&name=MIXEDEYE_1_575x375.jpg)
Tracking New Malware Threats
HYAS threat intelligence expert David Brunsdon discusses the latest malware threats, how we investigate them, and how to bolster your cyber defenses to protect your organization. In this webinar, see a live detonation of a popular malware family to understand how it is designed to breach your defenses. Then we show you how to stop it in its tracks with best practices for defense and investigation.
/iStock-1193827042_575x375.jpg?width=575&height=375&name=iStock-1193827042_575x375.jpg)
HYAS Products
With HYAS as your trusted partner in cyber threat hunting, security teams can expertly and proactively defend against cyber threats.
Protective DNS
Our protective DNS solution combines authoritative knowledge of attacker infrastructure and domain-based intelligence to proactively enforce security and block the C2 communication used by malware, ransomware, phishing, and other forms of cyber attacks.

Threat Intelligence and Investigation
HYAS Insight's flexible query language and customizable search parameters enable you to conduct thorough investigations tailored to your organization's specific needs, facilitating rapid decision-making and incident response. This is only the beginning!
Leverage HYAS Insight Cyber Threat Hunting Capabilities
HYAS Insight offers unparalleled access to a vast array of threat intelligence sources, including proprietary data feeds, open-source intelligence (OSINT), and dark web monitoring.

Identify Anomalies
Identify anomalies in your network traffic, system logs, or user behavior that may indicate potential security threats. With its advanced analytics capabilities, HYAS Insight helps you distinguish between normal and suspicious activities, allowing for targeted threat hunting.
Hypothesis-Driven Investigation
Develop hypotheses about potential threats based on known indicators of compromise (IOCs) or threat intelligence feeds integrated into HYAS Insight. Leverage its powerful investigative tools to validate hypotheses, gather evidence, and uncover the scope and impact of cyber threats.

Threat Actor Profiling
Create detailed profiles of threat actors, including their tactics, techniques, and procedures (TTPs) to anticipate their next moves, identify patterns and trends, and proactively defend against future attacks.

Collaborative Analysis
Foster collaboration within your organization by sharing insights, findings, and investigative workflows. Pooling collective expertise and resources enhances the effectiveness of your threat hunting efforts and strengthens your organization's security posture.
What Others Have to Say About Using HYAS Insight
Are you ready to harness the power of HYAS Insight to supercharge your cyber threat hunting efforts? Others have done so, and with great success.
HYAS Insight is our go-to resource, enabling us to connect the dots to rapidly investigate and understand threats affecting our clients. It is a core investigative tool that supports the core functions of the team which delivers complete threat intelligence to the client.
”Employing HYAS Insight has streamlined our investigations with an easy-to-use interface and needed contextual information. One pane of glass usually gives us what we need. HYAS Insight is typically our first pivot point on new investigations.
”Latest News & Resources
Securing the Modern Grid: Why Infrastructure Intelligence is Required for Critical Infrastructure
As global tensions rise and the energy sector undergoes rapid digital transformation, the stakes...
Continue ReadingUnpacking the Collins Aerospace Attack: Infrastructure Intelligence Lessons from Aviation Disruption
When most people think about critical infrastructure, they think about power grids, pipelines, or...
Continue ReadingTop 20 Blocked Destination Countries
HYAS blocks tons of queries on behalf of our clients each day and we occasionally step back and...
Continue Reading
Up Your Threat Hunting Game Today
With HYAS Insight as your trusted partner in cyber security, you can stay ahead of adversaries, mitigate risks, and safeguard your organization's digital assets with confidence and peace of mind. Defend against today's most advanced cyber threats and protect what matters most — your organization's reputation, intellectual property, and bottom line.


