HYAS Insight
HYAS Insight is an advanced infrastructure intelligence and cyber threat hunting platform that provides the tools to identify emerging threats, defend your operations, and deny the adversary.
Empower Your Security Teams
As one of the top cyber threat hunting tools, HYAS Insight provides unparalleled infrastructure intelligence. Give your security teams in-depth visibility into the resources being used by bad actors, know your adversary, and stop them in their tracks.

SOC Operations
Propel threat hunting, incident response, and SOC triage with actionable and relevant intelligence, recent malware infrastructure, and deep pivotability through our underlying Adversary Infrastructure Platform.
Cyber Threat Intelligence Program
Enable your CTI program with the context to better understand current and emerging threats. Then drive prioritized intelligence requirements and adversary profiling across your security teams to ensure improved organizational resiliency.

Fraud Investigations
Empower fraud investigators with new reach into fraudster infrastructure and ability to track activity across the internet. Aggregate infrastructure details, activity breadcrumbs, and actor identity to build cases and takedown packages.
Infrastructure Intelligence
Our threat infrastructure intelligence incorporates information about IP addresses, domains, and other resources on the internet that are utilized by bad actors to establish a base of operations for malicious activity, carry out attacks, and perform command and control operations. Ever-changing infrastructure is difficult to track and understand – this is where HYAS comes in.
HYAS validates, enriches, and transforms this information into proactive and relevant infrastructure intelligence that you can use to enhance your organizational security.

Verdicts, Related Infrastructure, and Bad Actor Insights
Whether you are kicking off your next threat hunt, building a better picture of an emerging threat, or understanding a persistent adversary’s changing behavior, there are some things that don’t change even if your investigations do. You are looking for actionable (V) verdicts on IOCs, clear mapping of (R) related infrastructure, and as many details about the threat (A) actor as possible. You are looking for VRA to rapidly profile the threat.

How One Large Bank Stopped a Russian Cyber Attack
HYAS received a request for assistance from one of the largest banks in North America. They were under a relentless credential stuffing attack targeting more than 13 million of their customer accounts. Using HYAS Insight, the security and fraud teams leveraged WHOIS information and passive DNS data to identify and counteract the threat.
/Russia%20case%20study_575x375.jpg?width=575&height=375&name=Russia%20case%20study_575x375.jpg)
Essential Threat Intelligence for a Leading Global MSP
HYAS Insight helped a Top 5 global professional services firm to connect and contextualize a wide range of datasets shared by multiple teams across the enterprise. This enabled swift detection and prevention of fraudulent activities, alongside DNS threat hunting across their clientele.
/Global%20MSP%20case%20study_575x375.jpeg?width=575&height=375&name=Global%20MSP%20case%20study_575x375.jpeg)
The HYAS Insight Advantage
The HYAS Adversary Infrastructure Platform is a data lake of infrastructure intelligence that HYAS uses to support its products. Our intelligence derives from proprietary and exclusive intelligence sources available only through HYAS, in addition to various restricted, commercial, and OSINT sources. HYAS transacts billions of data points daily and leverages this large footprint to provide unmatched infrastructure intelligence through the HYAS Insight portal and API.
HYAS Insight separates itself from other threat intelligence providers by combining a broad range of data types into a single solution. This helps HYAS Insight users get verdicts, related threat infrastructure details, and actor context more thoroughly and more quickly than what’s possible by piecing together information across many other tools.
If context is king in HYAS Insight, then pivoting is queen. HYAS Insight users can pivot through a wide range of data types to connect the dots and build an understanding of a threat. The solution provides bread crumbs along the way which can be saved, returned to, and branched on in order to support complex investigations.
Understanding the verdict, related infrastructure, and actor information for a single IOC is one thing, but what happens when you need an analysis on a set of IOCs representing a suspected campaign or distinct internet resources you believe could be related? HYAS insight’s Infrastructure Analysis is your go-to feature to analyze IOCs in bulk and get quick results to confirm your suspicions, help you identify patterns, and separate signals from noise.
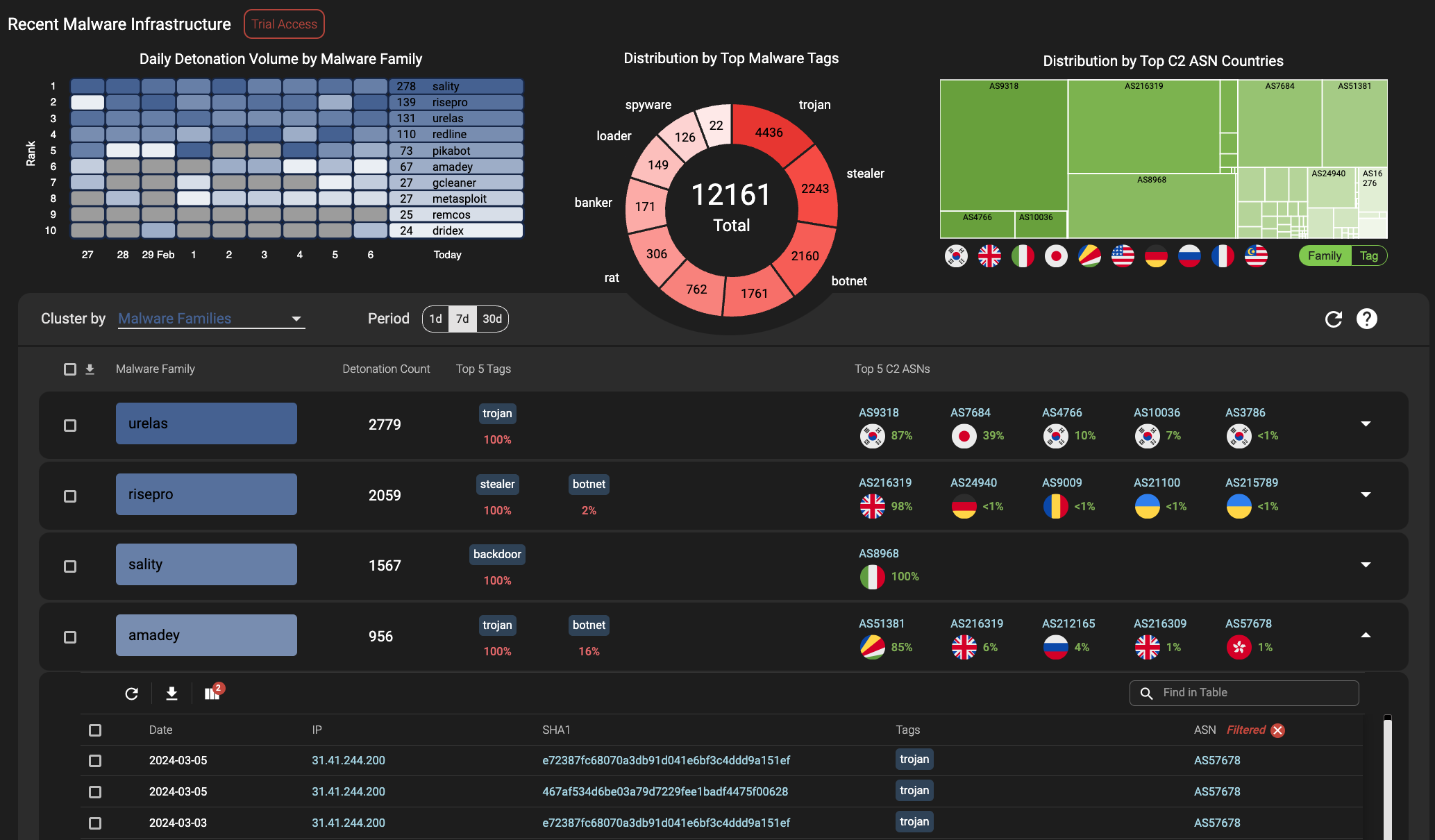
HYAS operates a continuous malware detonation pipeline to generate fresh infrastructure intelligence and assist your investigations and threat hunts. HYAS tags IOCs with malware family and type, aggregates tactical malware intelligence into higher-order grouping to identify patterns, and provides full malware analysis reports on detonated samples. In addition, our malware infrastructure dashboard constantly aggregates and displays malware intelligence based upon ASNs for C2 IPs, malware family, and more to help you seamlessly transition between high-level malware patterns and the granular infrastructure intelligence leveraged by malware.
No security outfit is the same. The intelligence requirements, the teams and tools to leverage the intel, and the budgets to pay for it are all highly variable. It’s for this reason that HYAS Insight offers a range of packages to align with your needs. We want to ensure you have the available intelligence types, product features, API volume, and other parts of the product that support you where you need it.
The HYAS Insight Intel Feed applies the same concepts from our Adversary Infrastructure Platform to the infrastructure associated with malware. It aggregates infrastructure intelligence for individual malware families, providing awareness of emerging threats that crosscuts distinct threat actors and attacks. We package this intelligence in unique ways to help you understand high-level malware patterns so you can aggregate the context and action the tactical intelligence for your SOC, CTI, and fraud teams. What’s more, it’s free. Check it outRegister for the free HYAS Insight Intel Feed..
HYAS Insight offers out-of-the-box integrations with a number of intelligence data providers, TIP, SOAR, SIEM, visualization, and cloud storage solutions. For full details, visit our integrations page. Plus, work with HYAS Insight data at scale to support the custom automation tasks required by your security organization.
Interested in learning more about HYAS Insight and the unique ways that infrastructure intelligence can equip your security organization? Contact our sales team!
Additional News & Resources
Securing the Modern Grid: Why Infrastructure Intelligence is Required for Critical Infrastructure
As global tensions rise and the energy sector undergoes rapid digital transformation, the stakes...
Continue ReadingUnpacking the Collins Aerospace Attack: Infrastructure Intelligence Lessons from Aviation Disruption
When most people think about critical infrastructure, they think about power grids, pipelines, or...
Continue ReadingTop 20 Blocked Destination Countries
HYAS blocks tons of queries on behalf of our clients each day and we occasionally step back and...
Continue Reading
See Our Threat Intelligence In Action
Our cyber threat hunting tools make it possible to detect and stop cyberattacks instantly with data and intelligence no one else has. Reach out to our team to get a personalized demo to see HYAS Insight in action.


