Hyas Blog | November 2023 Product Release News
November Product Release News
November marks an important milestone in the execution of a rich product roadmap for HYAS Insight. We are delivering on a significant component that is one part of an exciting path to a “next-gen” version of the solution.
The next-gen HYAS Insight is going to have better and more contextualized intelligence. It’s going to be easier to use and will have a “sizzle factor” that will mean a more delightful user experience. And it will proactively manufacture - not just require you to self-discover - custom insights aligned with your adversaries and your interests. But I am getting ahead of myself.
HYAS Malware Detonations
The milestone we’ve achieved this month is the re-tooling of our malware detonation infrastructure and the data pipeline that feeds many parts of HYAS Insight. This is important for several reasons.
First, we are now detonating and analyzing tens of thousands of malware samples per day on average. This new pipeline is higher volume and is expected to better align with real threats you’re dealing with on a daily basis. The resulting intelligence is not only timely, but we aim to make it as relevant and actionable as possible for you. In the end, our goal is to better align with your prioritized intelligence requirements and help you better protect your organization from your adversaries.
Second, we are correlating billions of hashes and C2 domains and IPs, which we then further correlate with other rich adversary infrastructure intelligence across the solution. A key area of improvement in this release is the more robust correlation and presence of malware intelligence in our Passive Hash and Malware Samples data sets across Insight. We’ve also added a new correlated Malware Samples tab for IP addresses in Insight.
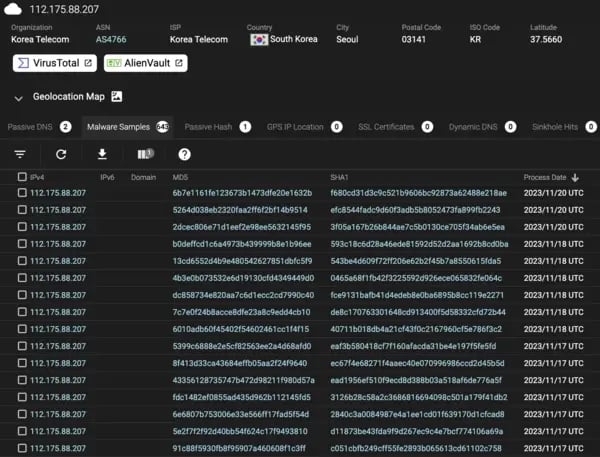
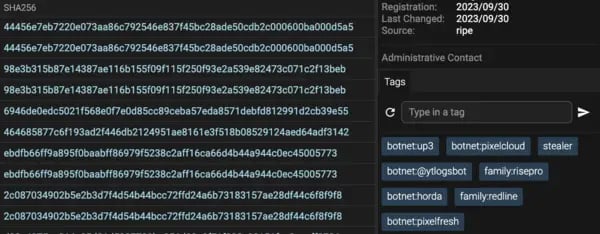
In addition, our malware analysis process is generating truckloads of context that improves the utility and visibility of Insight’s technical intelligence. Much of this context focuses on known malware families such as Lokibot, Smokeloader, and Mirai. But also includes rich context on Malware Type such as infostealers, backdoors, and botnets as well as adversary tactics, techniques, and procedures such as evasion. These obviously help paint a better picture of the threat and are accessed largely through what we call “system tags” (the blue ones). So watch out for tons of new context during your investigations in HYAS Insight.
And lastly, for this release we are populating a running list of our malware detonations and pivots through the technical intelligence in our Recent MW Infrastructure table.
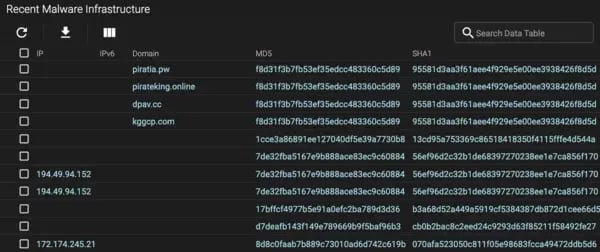
Yes, I know it is a chunky dataset but the intention - for now - is for this to serve as a repository of recent malware intelligence you can search against and pivot into. You can also export it to 3rd party tools for additional correlation and analysis. The emphasis here is on recency for now, but this will be changing in upcoming releases!
Back to [a Discussion of] the Future
There are a lot of exciting things coming on the product roadmap. One of the things we’ll be doing is further building on our malware intelligence foundation. In the next month or two, we are planning on dropping some really exciting ways for you to consume and make sense of this intelligence and action it in your organization. Here’s a sneak peak at one of those ways… sorry, we can’t reveal too much as our plans are still in motion!

We’re not just talking about improvements to the user interface when it comes to our malware intelligence. Sit tight, and we’ll provide more information soon!
We’re striving to better connect you with adversary intelligence that supports your workflows and helps you better defend your organization. So watch for some additional, exciting announcements from HYAS!
Learn More About HYAS Insight
HYAS Insight is an advanced threat intelligence and investigation platform that gives organizations the ability to identify, track, and attribute fraud and attacks faster and more efficiently.
By analyzing data aggregated from leading private and commercial sources around the world, HYAS is able to identify suspicious infrastructure likely to be used in attacks — sometimes months before it is even activated. Get unprecedented visibility into the origins of attacks, the campaign infrastructure being used, and the architecture likely to be used against you in the future.
HYAS Insight provides threat and fraud response teams with never-before-seen visibility into everything you need to know about an attack. This includes the origin, current infrastructure being used, alerts when new relevant infrastructure is created, and any infrastructure likely to be used against you in the future. Top Fortune 500 companies rely on our exclusive data sources and nontraditional collection mechanism to power their security and fraud investigations.
Further Reading
Examining Predator Mercenary Spyware with HYAS Insight
Elevate Your Threat Hunting with JARM
HYAS Insight Shines a Light on Financial Fraud
October 2023 Product Release Notes
September 2023 Product Release Notes
Book a demo today to find out what HYAS Threat Intelligence and Protective DNS solutions can do for your organization.
