Cyber Forensics & Incident Investigation
HYAS Insight is the premier solution for cyber security incident investigation. As one of the top digital forensics solutions, it equips cyber security practitioners with the tools and insights needed to stay ahead of threats and effectively mitigate security incidents.

Why Choose HYAS
Designed to facilitate cyber forensic investigation, HYAS Insight enables you to connect the dots, derive attribution, reveal correlations, and piece together the puzzle of cyber crimes.
Comprehensive Threat Intelligence
Identify attack vectors, malware signatures, and indicators of compromise (IOCs) to conduct thorough cyber forensic investigations and respond effectively. Track malicious IP addresses and domains and uncover patterns of suspicious activity.
Advanced Investigation Tools
Uncover the root causes of security incidents and trace malicious activities back to their source. From memory forensics to file analysis, HYAS Insight provides the capabilities needed to reconstruct cyber attacks, identify threat actors, and mitigate future risks.
Real-Time Monitoring and Alerting
Receive instant notifications on suspicious activities, anomalous behavior, or potential breaches, then respond swiftly to mitigate the impact of security incidents. Proactively detect and thwart cyber threats before they escalate into major incidents.
Collaborative Investigation Platform
Share insights, findings, and investigative workflows in real time, enabling cross-functional teams to work together seamlessly towards resolving security incidents.
HYAS Insight Empowers Your Cyber Security Forensics Efforts
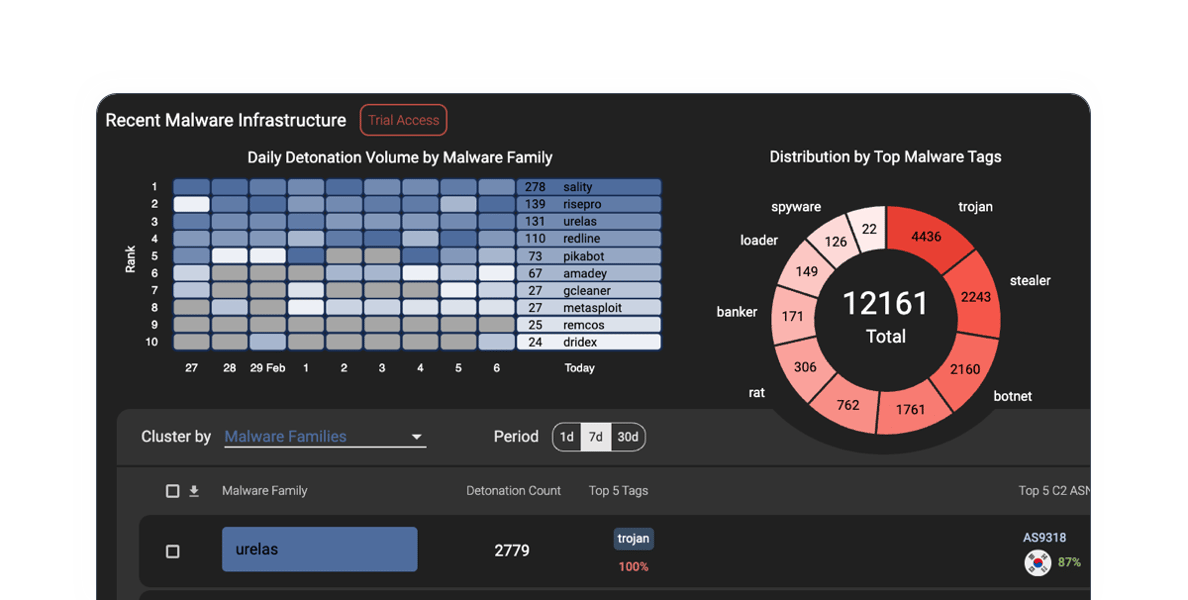
By leveraging advanced data visualization techniques and machine learning algorithms, HYAS Insight helps you make sense of complex datasets, identify patterns, and extract actionable insights that drive informed decision-making in incident response and mitigation efforts.
HYAS Insight allows you to integrate with SIEM platforms and threat intelligence feeds, providing continuous monitoring of your environment and enabling rapid detection and response to emerging threats. By providing a centralized platform for collaboration and information sharing, HYAS Insight ensures that all stakeholders are aligned and empowered to respond effectively to security incidents, minimizing the impact on your organization's operations and reputation.

Accelerating Investigations with HYAS Insight
The Anti-Human Trafficking Intelligence Initiative (ATII) needed an investigative tool that could help them close cases more quickly and accurately. Leveraging HYAS Insight’s consolidated and centralized data, as well as its advanced attribution and access to historical data, the organization was able to expedite case resolutions by weeks. They significantly reduced their case closure time and were able to aid people in desperate situations.

HYAS Shines a Light on Financial Fraud
HYAS provided a major national bank unprecedented visibility into the origins of cyberattacks against their institution, including the campaign infrastructure being used, and the architecture likely to be used against it in the future. Serving more than 8.5 million customers in business, retail, and other sectors worldwide, the bank turned to HYAS to protect their highly sensitive data from breaches, malware, fraud, and other cybercrimes.

HYAS Products
HYAS is your trusted partner in cyber security forensics, enabling security teams to proactively defend against cyber fraud with confidence and ensure business resilience.
Protective DNS
Our protective DNS solution combines authoritative knowledge of attacker infrastructure and domain-based intelligence to proactively enforce security and block the C2 communication used by malware, ransomware, phishing, and other forms of cyber attacks.

Threat Intelligence and Investigation
One of the top fraud protection solutions, HYAS Insight is an advanced threat intelligence and investigation platform that gives organizations the ability to identify, track, and attribute fraud and attacks faster and more efficiently.
Key Features of HYAS Insight for Cyber Forensics and Incident Investigation
Uncover hidden malware, detect memory-based attacks, and identify stealthy persistence mechanisms. Then, eradicate threats and restore the integrity of your systems.

File Analysis
Enable rapid response to security incidents by performing in-depth analyses of files and artifacts to identify malicious payloads, suspicious scripts, and indicators of compromise (IOCs). Identify malware variants, analyze malicious code, and extract forensic artifacts from files.
Memory Forensics
HYAS Insight makes it possible to analyze volatile memory to identify malware, malicious processes, and unauthorized activities, providing crucial insights into the tactics and techniques used by threat actors.

Fraudulent Network Traffic AnalysisDetection
Identify and mitigate security threats by monitoring and analyzing network traffic to detect and block anomalous behavior, command and control communications, and data exfiltration attempts.

Timeline Reconstruction
Reconstruct security incidents to visualize the sequence of events leading up to and following a security breach, aiding in root cause analysis and correlation of data sources to identify attack vectors and minimize impact across the organization.
Successful Cyber Incident Investigation Experiences
By correlating disparate sources of data, HYAS Insight helps you reconstruct the chain of events associated with a security incident, identify attack vectors, and determine the extent of the impact.
The HYAS speed of investigation was incredible. We were blown away by their responsiveness, knowledge, and expertise. To rapidly identify security issues in our infrastructure as well as find the culprits was astounding. HYAS jumped in and located the hacker in hours.
”HYAS Insight is our go-to resource, enabling us to connect the dots to rapidly investigate and understand threats affecting our clients.
”Employing HYAS Insight has streamlined our investigations with an easy-to-use interface and needed contextual information. One pane of glass usually gives us what we need. HYAS Insight is typically our first pivot point on new investigations.
”Latest News & Resources
Securing the Modern Grid: Why Infrastructure Intelligence is Required for Critical Infrastructure
As global tensions rise and the energy sector undergoes rapid digital transformation, the stakes...
Continue ReadingUnpacking the Collins Aerospace Attack: Infrastructure Intelligence Lessons from Aviation Disruption
When most people think about critical infrastructure, they think about power grids, pipelines, or...
Continue ReadingTop 20 Blocked Destination Countries
HYAS blocks tons of queries on behalf of our clients each day and we occasionally step back and...
Continue Reading
Get Started Today
Ready to elevate your cyber forensics and incident investigation capabilities? With HYAS as your trusted partner, you can enhance your organization's cyber resilience, mitigate security incidents, and protect critical assets from evolving cyber threats.


