Hyas Blog | 2020 Verizon Data Breach Investigations Report
The Verizon Data Breach Investigations Report 2020 was published in mid-May and makes for some interesting and entertaining reading (the footnotes can be very funny). The DBIR runs 119 pages this year and a couple of themes caught my eye.
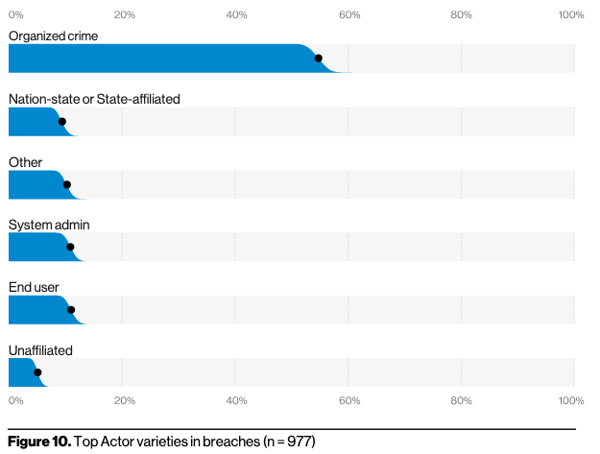
One theme is that organized crime is the big threat to enterprises. Making an illicit profit is the major driver behind the vast majority of breaches described in the 2020 DBIR. Script kiddies and nation-states are minor when compared to organized criminal gangs. If you want to make the biggest impact in improving your security, understanding who the bad actors are that are attacking you and countering them will get you the biggest bang for your IT security buck.
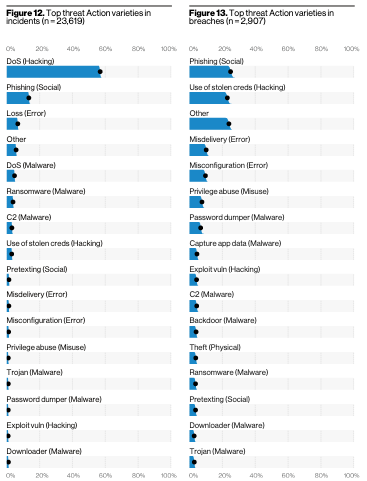
Looking at the methods used by bad actors, practically all of them have something in common. Bad actors need to leverage a domain to perpetrate their crimes. That means that there is a DNS element to practically all of the incidents and breaches in the DBIR. There are exceptions like physical theft and misconfiguration, but the other varieties, from social to malware, all need a domain and thus utilize DNS to do their dirty work. If malware talks to a command and control (C2) server, it needs a domain to contact. DNS is the unstated choke point for most of the incidents and breaches listed in this and past DBIRs.
So what can you do knowing that organized crime is your major adversary, and the adversary uses DNS? Bad actors who are waging their illegal campaigns against enterprises need to establish the domain infrastructure for their attacks well before they launch their attacks. Understanding the adversaries and their infrastructure permits you to preemptively block the attack before it executes.
IT security folks have a complex infrastructure to protect and a blizzard of incoming telemetry to sift through. Understanding how adversaries are using domains can help block future attacks. What’s more, your DNS egress traffic provides a high fidelity signal that can improve your overall security.
HYAS can help you along the way. HYAS Insight enables analysts to see what their adversaries are doing and frequently drives attribution “to the doorstep”. HYAS Protect preemptively blocks attacks at the network, protecting your infrastructure and feeding your other tools with precise information about attacks and compromised systems. Give us a shout to learn more.
