Hyas Blog | HYAS Protect Integration with Microsoft Defender for Endpoint
HYAS Protect provides a leap forward by utilizing authoritative knowledge of attacker infrastructure including unrivaled domain-based intelligence to proactively protect Microsoft Defender for Endpoint deployments from network-based cyberattacks. HYAS Protect augments Defender for Endpoint’s security by analyzing Defender for Endpoint sensor data to detect communication with malicious URLs/domains and enabling those domains to be blocked.
HYAS Protect delivers verdicts on URLs/domains to block command and control (C2) communication used by malware, ransomware, botnets, and supply chain attacks as well as block phishing attack communication. HYAS Protect combines infrastructure expertise and multi-variant communication pattern analysis to deliver reputational verdicts for any domain and infrastructure, allowing Defender for Endpoint to preempt attacks at the network layer.
The Threat: Phishing and Command and Control Domains
Adversaries launching malware, ransomware or supply chain attacks, or attackers trying to phish credentials, need to pre-stage the C2 or phishing infrastructure. HYAS Protect integrates with Defender for Endpoint to identify that infrastructure and enable blocking actions.
Microsoft Defender for Endpoint - HYAS Protect Process Flow
Devices send telemetry to Defender for Endpoint, and the Defender for Endpoint subscription is configured to send telemetry to a Microsoft Azure Event Hub. HYAS Protect retrieves telemetry from Azure Event Hub and processes device events. If malicious traffic is identified, HYAS Protect updates Defender for Endpoint to start blocking the IP addresses or URLs/domains, and alerts the customer. Below is the process flow for events from Defender for Endpoint being analyzed and indicators of compromise (IoCs) being returned for traffic evaluated by HYAS Protect to be malicious (see Figure 1).
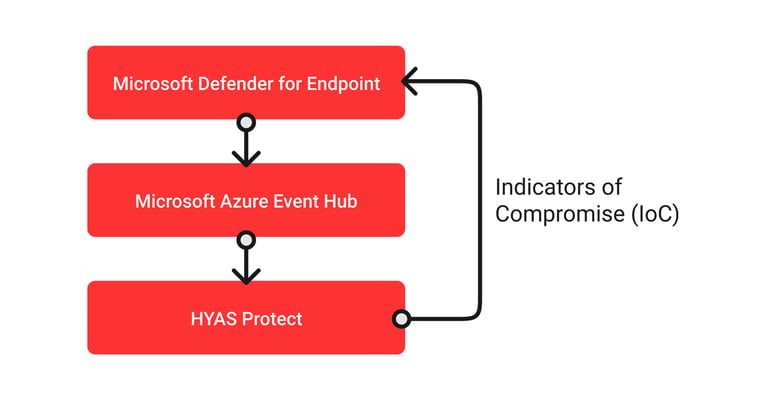
(Figure 1: Microsoft Defender for Endpoint-HYAS Protect integration process flow)
Administrators can configure Defender for Endpoint to export the Defender for Endpoint data in the Microsoft Defender Security Center “Data export settings.” Endpoint data exports occur in batches and latency can vary based on factors such as device battery life and network connectivity.
Defender for Endpoint delivers device events to the Azure Event Hub, and HYAS Protect in turn evaluates the URLs/domains and IP addresses in the event stream. Using HYAS Protect’s extensive data lake of adversary infrastructure, analysis of adversary communication patterns, and the HYAS Protect Watch Engine to evaluate suspect domains, HYAS Protect renders verdicts on URLs/domains and IPs.
URLs/Domains or IP addresses that are determined to be malicious are included as an Indicator of Compromise (IoC) and subsequently blocked by Defender for Endpoint.
