Hyas Blog | Recent Ursnif Campaign Infrastructure - What to Keep an Eye On
In recent months, there are has been a resurgence of Ursnif (aka Gozi ISFB) related campaigns. Since 2014, when the source code for the one of the more popular banking trojans was leaked, adversaries have been busy at work adding new features and capabilities to the malware. Some of these features and functions were highlighted in a recent blog by Cybereason, outlining the changes and new functions found. Another by SentinalOne highlights some of the polymorphic features of Ursnif.
As with many actors and groups, they don’t tend to limit themselves to just one malware family, and so understanding and being able to correlate additional adversary infrastructure becomes incredibly important to protect against additional attacks. Looking at the infrastructure related to this campaign and using a few of the data pivot points in Comox allows us to have a fuller view of what is at the actor’s disposal.
Reviewing the identified C2 IOCs, we can start to map out additional attack infrastructure and other binaries that the actors have used. Examining the whois records related to the C2 domains, we can see over 500 other domains controlled by the same actor. The next step that can be very helpful is to look at sometimes under-utilized data points like telephone numbers that are related to the same actor. Using another handy feature in Comox, we can use “HLR” data (Home Location Register) to identify the Russian cellphone associated with the actor and then pivot off of it to identify additional assets. This produces 4 additional email addresses tied to the same actor, bringing the total number of domains to over 680. From here we can query to see what malware has been seen related to the actor’s newly discovered infrastructure, and sure enough, they don’t just limit themselves to Ursnif, not by longshot. To date, the actors have used 170 different binaries covering a host of different malware families.
While some actors are more advanced than others, most are incredibly persistent, and this is why understanding all the tools at their disposal is critical to blocking future attacks. They aren’t going to take their toys and go home if they aren’t successful the first time around; if they can’t get you one way, they will try another, and another, and another.
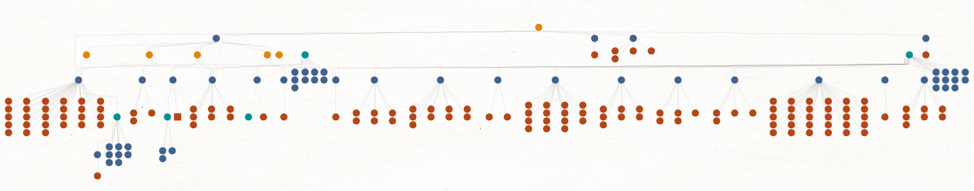
Graphing the data within Comox, a full picture of the adversary’s infrastructure and related malware can be seen. All from, just a few starting IOCs.
