Hyas Blog | Exploring a Lokibot and Azorult Actor’s Infrastructure
Investigating attacker infrastructure is the bread and butter of HYAS Comox. One of the routine tasks we need to do as investigators and analysts is to find malware samples and infrastructure related to a given incident or report. Comox makes this task quick and painless, especially when combined with our Maltego transforms.
In this post, we’ll walk through an example of enumerating malware samples and domains related to IOCs found doing OSINT research.
In the first example, our investigation starts with a report on Twitter of some deployed Lokibot and Azorult admin panels, and a link to a Pastebin post listing the URLs of the panels. A few of these URLs were reported by other Twitter users as well.
Reference tweet: https://twitter.com/ViriBack/status/1134662952898965504
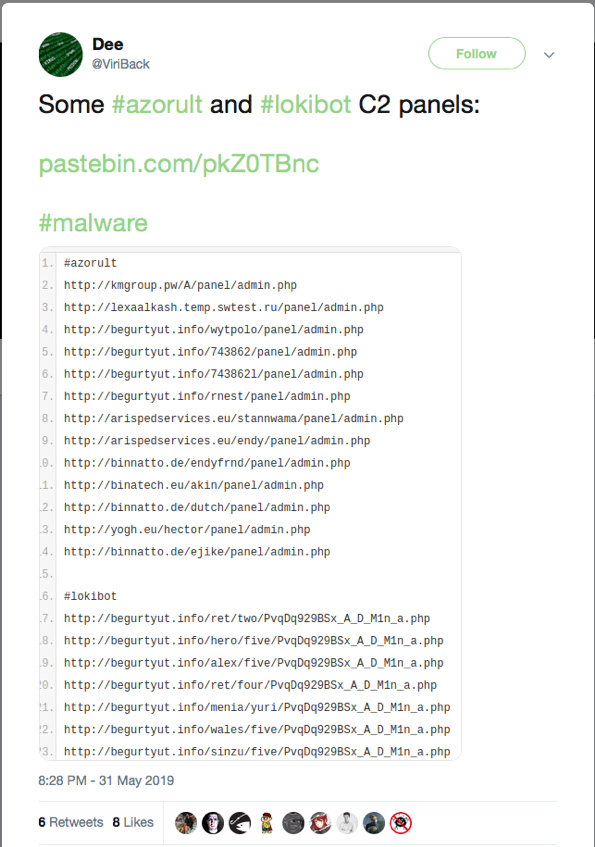
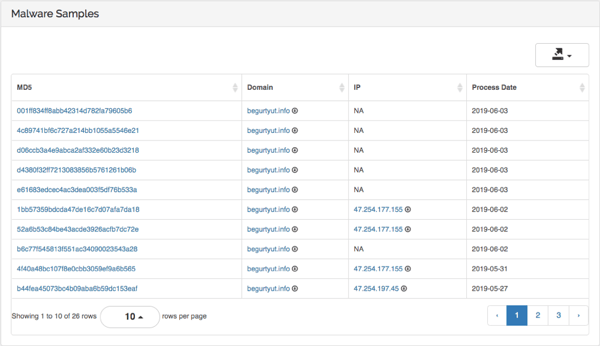
One of the domains that immediately pops out is begurtyut[.]info, which appears in the Lokibot and Azorult lists. One common task when investigating an incident is attempting to locate related malware samples to a given IOC. Unfortunately, the reference tweet does not list the corresponding malware samples for the admin panels, which is often useful in an investigation. If we jump into Comox to investigate this domain further, we immediately see 26 related malware samples, all processed around the same time as the initial tweet (31 May 2019).
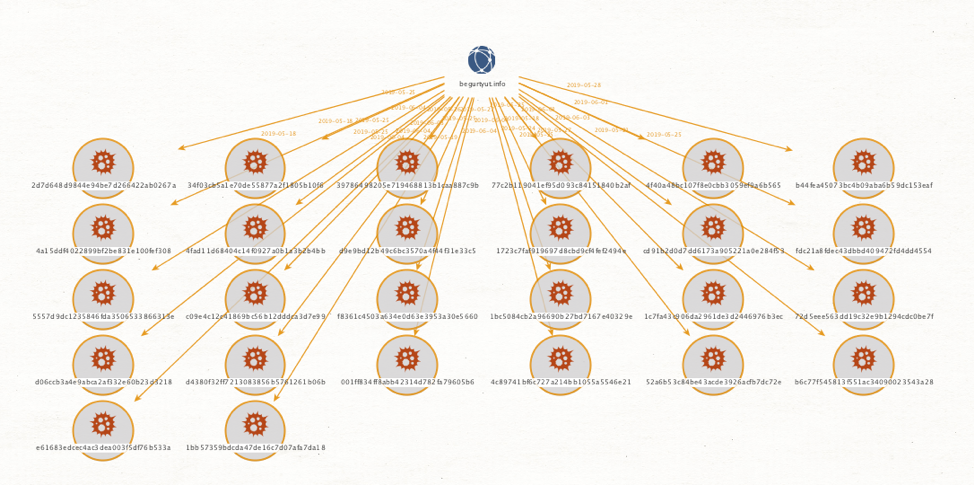
Here’s what it looks like in Maltego:
We can investigate the reported domains further in Comox by looking at shared infrastructure. By using the Passive DNS functionality of Comox, we can expose a number of IP addresses associated with begurtyut[.]info. We can quickly see some shared infrastructure with some of the other domains reported in the Pastebin post including beautynams[.]com. The IP addresses in use appear to be VPS hosting on Alibaba Cloud Services and Reg.ru.
Pivoting further using Comox’s Passive Hash functionality exposes 10 more domains, with hundreds of additional malware samples. In addition to Azorult and Lokibot, the new set contains what appears to be Pony Loader samples as well.
Another pivot from these new domains to registrant email address, we are able to recover a number of suspected actor email addresses. Examining the domains registered by these registrant email address to registered domain returns another 42 suspicious domains, a number of which are suspended, including names like cashoutsquad[.]com, bigfunds[.]xyz and cashfingers[.]net. This also exposes a few potential actor-maintained phone numbers with a Nigerian country code that appear to be active. The newly discovered domains lead to over a hundred additional malware samples used in similar campaigns over the same timeframe.
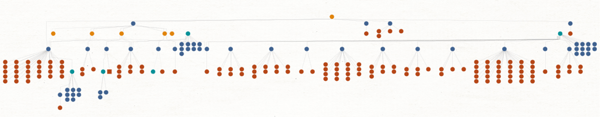
Here’s what the final graph in Maltego looks like. Yellow nodes are IP addresses, red nodes are malware samples, blue nodes are domains and green nodes are email addresses.
Comox allows users to proactively monitor any IOC’s such as email addresses and phone numbers for new potentially malicious domains created domains by suspected actors. It’s clear in this case that the actors are re-using the same email addresses and infrastructure which makes ongoing and monitoring and blocking an effective countermeasure.
In summary, by starting from a single piece of open source intelligence (OSINT) containing only a handful of URL’s, we can quickly pivot using Comox to dozens of domains, hundreds of related malware samples, as well as IP addresses, phone numbers and registrant email addresses. Comox allows users to proactively monitor any IOC’s such as email addresses and phone numbers for new potentially malicious domains created domains by the suspected actors.
