Hyas Blog | Putting an End to Emotet: Measuring the Efficacy of Protective DNS
We compared HYAS with other top protective DNS providers to find out which one was able to detect and block the most domains associated with an Emotet attack.
Anyone who is plugged into the cybersecurity world has already heard plenty about Emotet, but that doesn’t make it old news. Check Point’s 2022 Cyber Attack Trends: Mid-Year Report reveals that Emotet is still the most widely used malware overall. (It dropped in 2021 but had a resurgence in 2022). In fact, CISA has labeled Emotet “among the most costly and destructive malware,” in use today. Those are some truly frightening assessments that make it clear an Emotet infection is still a major headache for any company.
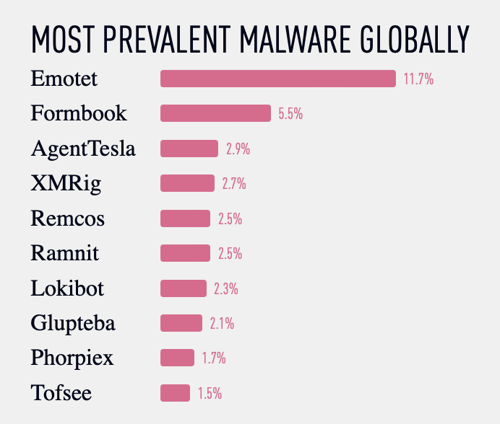
Scource: Check Point 2022 Cyber Attack Trends: Mid-Year Report
Emotet debuted in 2014 as a banking trojan, but over the years it has morphed significantly and continues evolving to this day. It is now primarily used as a dropper/loader, deploying other modules or payloads after infection.
Initial exposure generally occurs via malspam when a user engages with an email containing a malicious attachment or link, such as a PDF or Word document containing macros. After initial infection, Emotet will reach out to a command and control (C2) server to report its successful infiltration and receive instructions before deploying or using its payloads or modules.
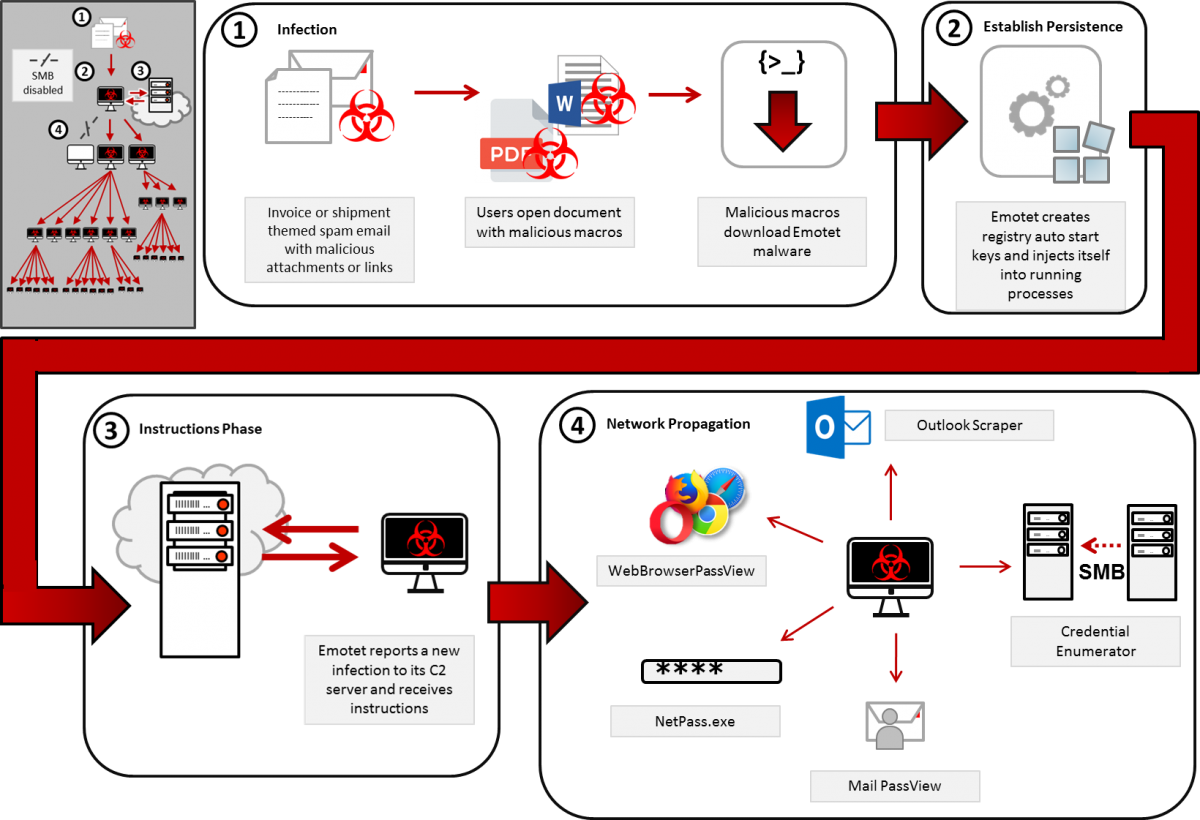
Scource: Cybersecurity & Infrastructure Security Agency (CISA)
Protective DNS services can detect and block Emotet during the initial infection, when Emotet attempts to reach out to its C2 server. This blog focuses on using this window of time as an opportunity to notice the infection and shut it down.
Emotet is used by many threat actors and during different campaigns for the same threat actor. This means that the infrastructure Emotet communicates with, such as C2 servers, differs from actor to actor, campaign to campaign, target to target. There is no static set of domains that can be blocked to neutralize Emotet, making it very important that the Protective DNS service used is able to determine whether a domain is malicious before it has been used in the wild.
Like other protective DNS providers, HYAS uses DNS as the enforcement mechanism to block malicious domains. However HYAS does not limit itself to known indicators or common algorithms and anomalies. More importantly, HYAS's approach includes mapping and understanding threat actor infrastructure before the threat actor uses that infrastructure in the wild. This ability, along with HYAS's unrivaled domain intelligence, enables HYAS to block malicious traffic like Emotet from accessing that infrastructure the first time it gets used.
Using a real-life, in-the-wild Emotet campaign, we compared results from several top protective DNS providers to evaluate their ability to block new threats.
Products Tested:
- HYAS Protect
- DNSFilter (Enterprise version)
- Cisco Umbrella DNS Security Advantage
- Quad9
Test Domains
The threat intelligence team at HYAS was doing investigations into a campaign that used Emotet and extracted a list of domains Emotet was communicating with during that campaign. This resulted in a list of 76 domains. Of these 76 domains, there were only two FQDNs that were legitimate to communicate with, namely:
- x1.c.lencr.org
- r3.o.lencr.org
Both of these are owned by Let’s Encrypt and are used to verify if certificates issued by Let’s Encrypt are still valid. The first one hosts their CRL and the second is used for OCSP, both ways to verify certificate validity.
This leaves 74 domains without a valid reason for traffic, though Emotet was actively reaching out to these domains.
Please note that this list of domains was not added to any HYAS product prior to testing to ensure that it didn’t have an unfair advantage and could only use the knowledge we already had about malicious domains and threat actor infrastructure.
Test Methodology
We tested twice. When we received the list from our threat intelligence team, as well as 4 weeks later to see what changed.
HYAS, DNSFilter, and Cisco Umbrella were all set to their most stringent security configurations, blocking all malicious traffic and newly registered domains. Uncategorized domains were not blocked. Although blocking uncategorized domains would increase all vendors’ numbers, it would also result in too many false positives (and frustrated users) to be useful in most real-world environments.
For Quad9, no configuration is possible as this is not a service targeted at enterprise users, but is still included here nonetheless as a reference point.
A script would take each domain from the list of 74 domains and do an actual DNS lookup with each of the protective DNS solution providers, as well as do an API call to VirusTotal. The results were tallied as follows:
- If the service returned an IP address of a block page, the DNS request was considered blocked.
- If the service returned an NXDOMAIN, the DNS request was considered blocked.
- If the service timed out, the DNS request was considered blocked (note that not a single DNS request to any of the providers was timed out, but the script had provisions for detecting this).
- If the service returned an IP address that was not of a block page, the DNS request was considered allowed.
VirusTotal aggregates information from 94 different security vendors to determine a domain’s risk score. A vendor can flag a domain as:
- Malicious
- Suspicious
- Harmless
- Undetected
- Timeout
For the VirusTotal score of a domain, we combined the number for “Malicious” and “Suspicious”. For example, if a domain gets flagged by three vendors as “Malicious” and two vendors as “Suspicious”, its VirusTotal Score would be five.
If the VirusTotal score is zero, none of the 94 vendors VirusTotal uses flagged the domain as “Malicious” or “Suspicious”.
Initial Results
After running the 74 domains through each protective DNS solution, these are the outcomes:
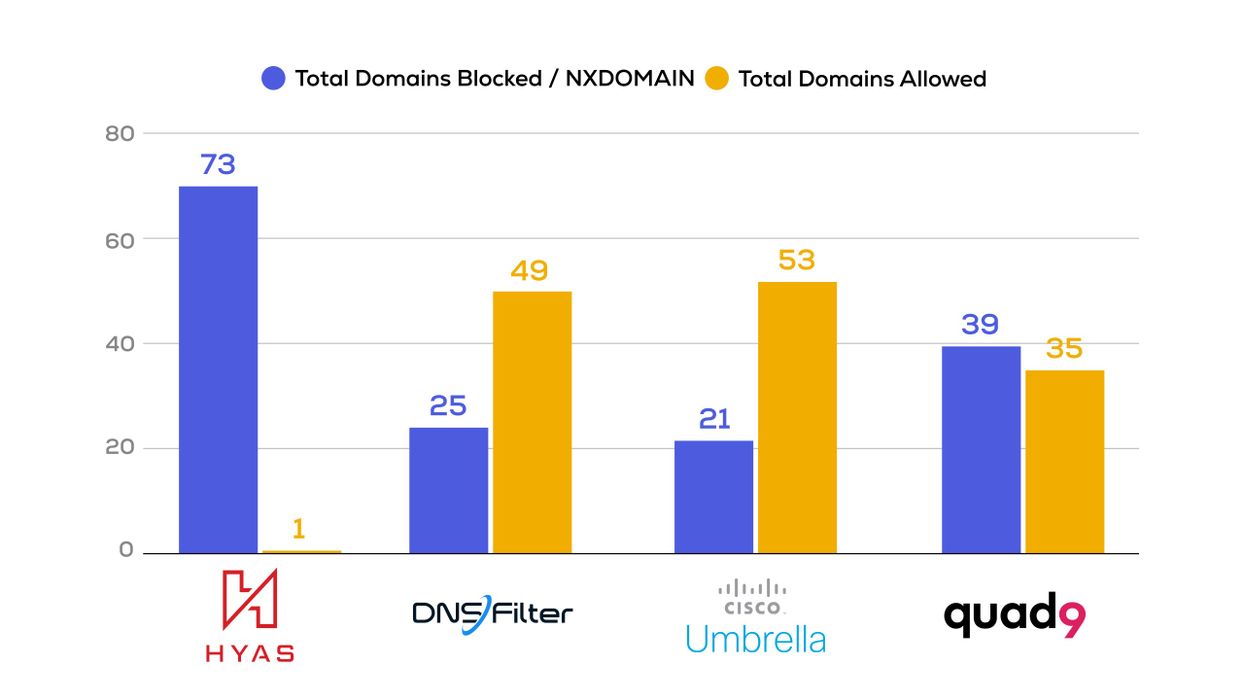
There is no single security solution that will block all malicious traffic. The results for DNSFilter and Cisco Umbrella are very similar, though Quad9 posts better results than those two. However, HYAS Protect blocked more malicious domains by a large margin than its competitors.
Since this was already an Emotet campaign that had been going on, there were only 5 domains that had a VirusTotal score of 0, signifying that most domains had been known to be malicious by at least one vendor used by VirusTotal. The range of VirusTotal scores was from 0 to 16 vendors flagging domains as suspicious or malicious.
Updated Results After Four Weeks
We ran the 74 domains through all the protective DNS solutions again four weeks after the initial test to see what changed. Here are the results:
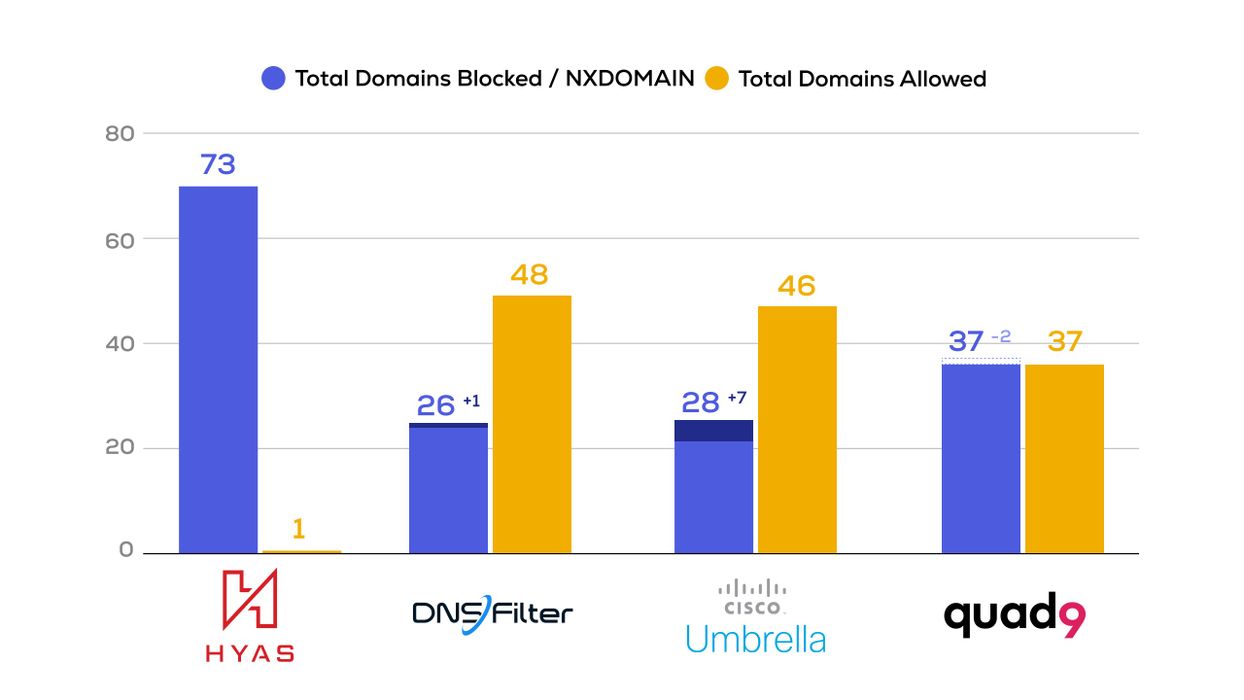
HYAS’s results stayed the same, while both DNSFilter and Cisco Umbrella started blocking more domains, with Cisco Umbrella showing the bigger improvement. Strangely, Quad9 started allowing two more domains.
Conclusion
Having a protective DNS solution in place is valuable for stopping and containing breaches. DNS resolution is one of the first steps most malware or threat actors will do and makes it a great time to detect and/or block traffic. However, as shown here, it is important to use a protective DNS solution that doesn’t look at domains on their own, but also understands their relationships to determine if they are part of a threat actor infrastructure, even before the domains are used maliciously. HYAS is able to provide a much higher catch rate, especially for domains that are not yet known to be malicious — providing demonstrable proof of proactive protection.
